THIS ARTICLE IS ABOUT A NEW FORM OF PHISHING CALLED DESKTOP PHISHING, TO KNOW ABOUT PHISHING- CLICK
TO KNOW HOW TO CREATE A PHISHING PAGE- CLICK
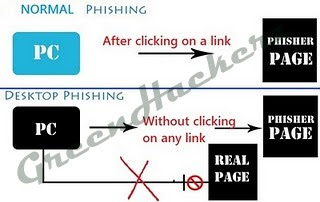
In PHISHING :-
1. Attacker convinces the victim to click on the link of fake login page which resembles a genuine login page.
2.Victim enters his credentials in fake login page that goes to attacker
3.Victim is then redirected to an error page or genuine website depending on attacker.
3.Victim is then redirected to an error page or genuine website depending on attacker.
But main drawback in phishing is that victim can easily differentiate between fake and real login page by looking at the domain name. We can overcome this in desktop phishing by spoofing domain name.
In DESKTOP PHISHING :-
1. Attacker sends an executable/batch file to victim and victim is supposed to double click on it. Attacker's job is done.
2. Victim types the domain name of orignal/genuine website and is taken to our fake login page. But the domain name remains the same as typed by victim and victim doesn't come to know.
3. Rest of the things are same as in normal phishing.
DESKTOP PHISHING
1) Modify hosts file
2) Compress and Bind it with an exe such that when he clicks on it the modified hosts file gets replace in the victims "\system32\drivers\etc" directory
3) Host the phishing page on your computer using server software such as wampserver.
4) When the victim tries to reach Paypal or a similar site from their computer, they are of course taken
to the phish page running on the attackers PC which will still say "Paypal.com" in the address bar.
When the victim enters their details, they're actually placing them directly onto the attackers computer
OK Now Lets Start..
Step 1: Modify hosts file
Go to C:\Windows\System32\drivers\etc
There you will find the hosts file which will look something like this -






